There has been a recent security vulnerability discovered with the Java component / software that could allow unauthorized access to computers. As a result, it is critical that you update the Java on your computer with the latest version from Oracle.
Downloading the latest version of Java
You can download the latest version at http://www.Java.com. Before you download and install the latest version of Java, please be sure to remove any / all older versions from your computer. More information on this can be found at http://java.com/en/download/faq/remove_olderversions.xml.
Issue in Firefox when uploading images
Once you remove any / all older versions of Java from your computer and install the latest version, you may experience the following in Firefox when uploading images to any "Photo Gallery" Page Type or when uploading images and files to your Products. You may see the following screen / window (see Screenshot # 1 below), and eventually after waiting about a minute or so, you will get a message saying that "This plugin has security vulnerabilities. Click here to activate the Java(TM) Platform SE 7 U plugin." (see Screenshot # 2 below).
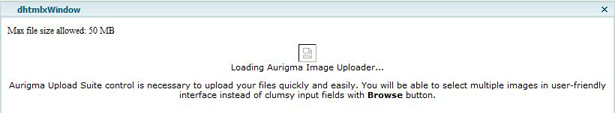 Screenshot # 1
Screenshot # 1
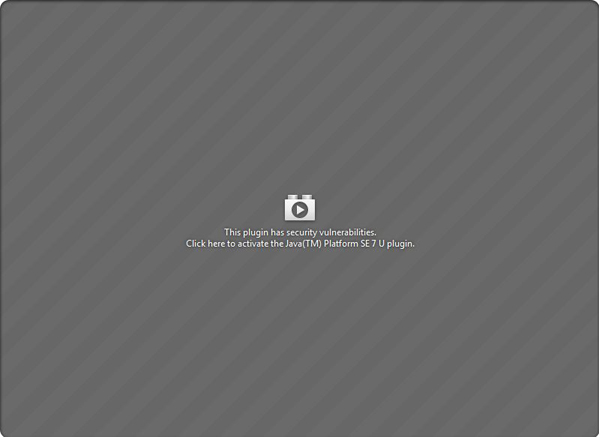 Screenshot # 2
Screenshot # 2
If you click on the message to activate Java, the uploader will come up and you will be able to upload your images / files. However, the next time you need to upload an image / file, you will have to wait again until that message comes up and will then have to click the message to activate Java in order for the uploader to come up.
Bypassing the Security Vulnerability message - "This plugin has security vulnerabilities. Click here to activate the Java(TM) Platform SE 7 U plugin."
You can bypass this security vulnerability message for your COOLSite Admin only, and have the uploader come up immediately every time you need to upload an image / file, by doing the following once this message appears.
- Click on the red Lego icon next to the address bar in Firefox. You may see this icon next to the main address bar or the address bar of the pop-up window (see Screenshot # 3 below). You will then see the following screen upon doing so (see Screenshot # 4 below).
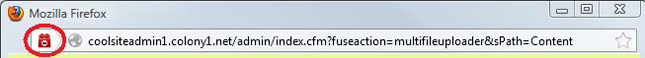 Screenshot # 3
Screenshot # 3
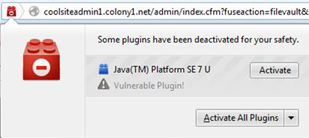 Screenshot # 4
Screenshot # 4
- Select "Always activate plugins for this site" from the drop-down selection box.
- The uploader will now come up and you will be able to select and upload your images / files.
Please note that by doing the above, Firefox will remember your preference. Therefore, every time you have to upload an image / file again, the uploader will come up immediately (bypassing the "This plugin has security vulnerabilities. Click here to activate the Java(TM) Platform SE 7 U plugin." message) and you will not have to repeat the above steps again.
Resetting the Plugin Security Vulnerability Warning message in your COOLSite Admin
If for some reason you would like to reset the plugin security vulnerability warning message in your COOLSite Admin, you will need to do the following (see below). However, by doing the below, you will also be removing your browser's cache files associated with your COOLSite Admin, as well as your saved password (if you have your password saved when you login to your COOLSite Admin).
- Type "about:permissions" in the address bar in Firefox.
- Once this page comes up, you will notice a search box in the upper left corner (see Screenshot # 5 below).
 Screenshot # 5
Screenshot # 5
- Type "coolsiteadmin1.colony1.net" (without the quotes) into the search box and you will see one entry directly under the search box.
- Click on that entry and you will notice on the right-side of the page (at the top), it says "Permissions for coolsiteadmin1.colony1.net".
- Towards the far right of that heading, you will see a button for "Forget About This Site", which you will need to click on.
- You can now close this tab / window. The next time you try to upload an image / file, you will see the plugin security vulnerability warning message again (assuming that the Java plugin is still vulnerable).
If you have any questions regarding the above, please let us know. Thanks!